Encrypted file-system can be easily created using cryptmount. On Ubuntu/Debian you can install cryptmount using “sudo apt-get install cryptmount”.
In this example I will demonstrate how to create an encrypted file-system on a flash drive and then use it on another machine. You will need root privileges on machines where you want to create or access this file-system. First we need to create the file system on the flash drive. To do this create an entry in the /etc/cryptmount/cmtab like this
cryptusb { dev=/media/flash/cryptusb.fs
dir=/home/adnan/cryptusb
fstype=ext3
fsoptions=defaults
cipher=aes
keyfile=/media/flash/cryptusb.key
keyformat=builtin
}
This tells cryptmount that your file-system name is cryptusb and you want to store your file-system in /media/flash/cryptusb.fs and to mount it to /home/adnan/cryptusb. It also tells it that the filesystem type is ext3 and to use AES algorithm to encrypt/decrypt the file-system. You can change cipher filed to change the encryption algorithm. Its important that the keyfile and dev are flash drive paths because other wise your file system wont reside on your flash drive and hence you wont be able to use it on any other machine. man cmtab has more information on all the available fields and their valid values.
Now create the file(specified in dev field) which will contain this encrypted file system and the mount point.
$ dd if=/dev/zero of=/media/flash/cryptusb.fs bs=1M count=32
32+0 records in
32+0 records out
33554432 bytes (34 MB) copied, 0.673204 s, 49.8 MB/s
$ mkdir /home/adnan/cryptusb
Next generate the encryption key. You will need to specify key size in bytes
$ cryptmount --generate-key 32 cryptusb
generating random key; please be patient…
enter new password for target "manual":
confirm password:
Now issue following commands to prepare and format the file-system:
$ cryptmount --prepare cryptusb
enter password for target "cryptusb":
$ mkfs.ext3 /dev/mapper/cryptusb
$ cryptmount --release cryptusb
The file-system is now ready and can be mounted using command “cryptmount cryptusb”. To unmount use “cryptmount –u cryptusb”. To use this file-system on another machine just copy
cryptusb { dev=/media/flash/cryptusb.fs
dir=/home/adnan1/cryptusb
fstype=ext3
fsoptions=defaults
cipher=aes
keyfile=/media/flash/cryptusb.key
keyformat=builtin
}
to /etc/cryptmount/cmtab on other machine. Change path in dev and keyfile fields to path to cryptusb.fs and cryptusb.key if flash drive on this machine is not mounted as /media/flash. You can also change dir field if you want the file system to be mounted some where else. After adding this to /etc/cryptmount/cmtab save the file and issue follwing commands
$ cryptmount --prepare cryptusb
$ cryptmount --release cryptusb
and you are done. you can now mount and unmount the file system using cryptmount. You may face some problem accessing files and directories because of file permissions. You can always change file and directory permissions using “chmod” and “chown” commands. A simple workaround is to make root to be the owner of this filesystem. To do this mount this file system using “cryptmount cryptusb” then issuing command “chown root:root /home/adnan1/cryptusb”. Then you can access this file system as root on both machines. This way you wont have to change permissions whenever you take this filesystem from one machine to other.
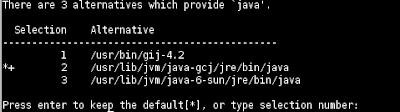 The * sign means that this JVM is default. Enter the number for Sun JRE which in my case is 3. Now you can check your java version using: java -version
The * sign means that this JVM is default. Enter the number for Sun JRE which in my case is 3. Now you can check your java version using: java -version